Security Insights
Deep dives, expert analysis, and practical guidance on exposure management, adversarial validation, and the future of AI-driven security operations.
Major Data Breach at Allianz Life: What Happened, Who Was Affected, and What You Can Do
Hackers have accessed personal information tied to most of the 1.4 million customers of Allianz Life Insurance Company of North America, according to a statement issued by its parent company. On July 16, 2025, a malicious threat actor gained access to a third-party cloud-based CRM system used by All

Strobes New Feature: Full Control Over Risk-Based Prioritization
Every security team knows the struggle: You've got hundreds (or thousands) of vulnerabilities, limited resources, and the constant question – "What should we fix first?" CVSS scores? They're a start, but they don't know that your payment processing system is more critical than your internal wiki. Tr

The CEO's Chronicles | When Nobody Believed - The 2022 Rejection Story (Part 1)
From Rejection to Recognition - The Strobes Journey The email was short. Brutal in its simplicity. It was the seventh rejection in three months. Seven different ways of hearing the same message: Nobody believes in your vision. As I sat in my office that evening in late 2022, staring at yet another p
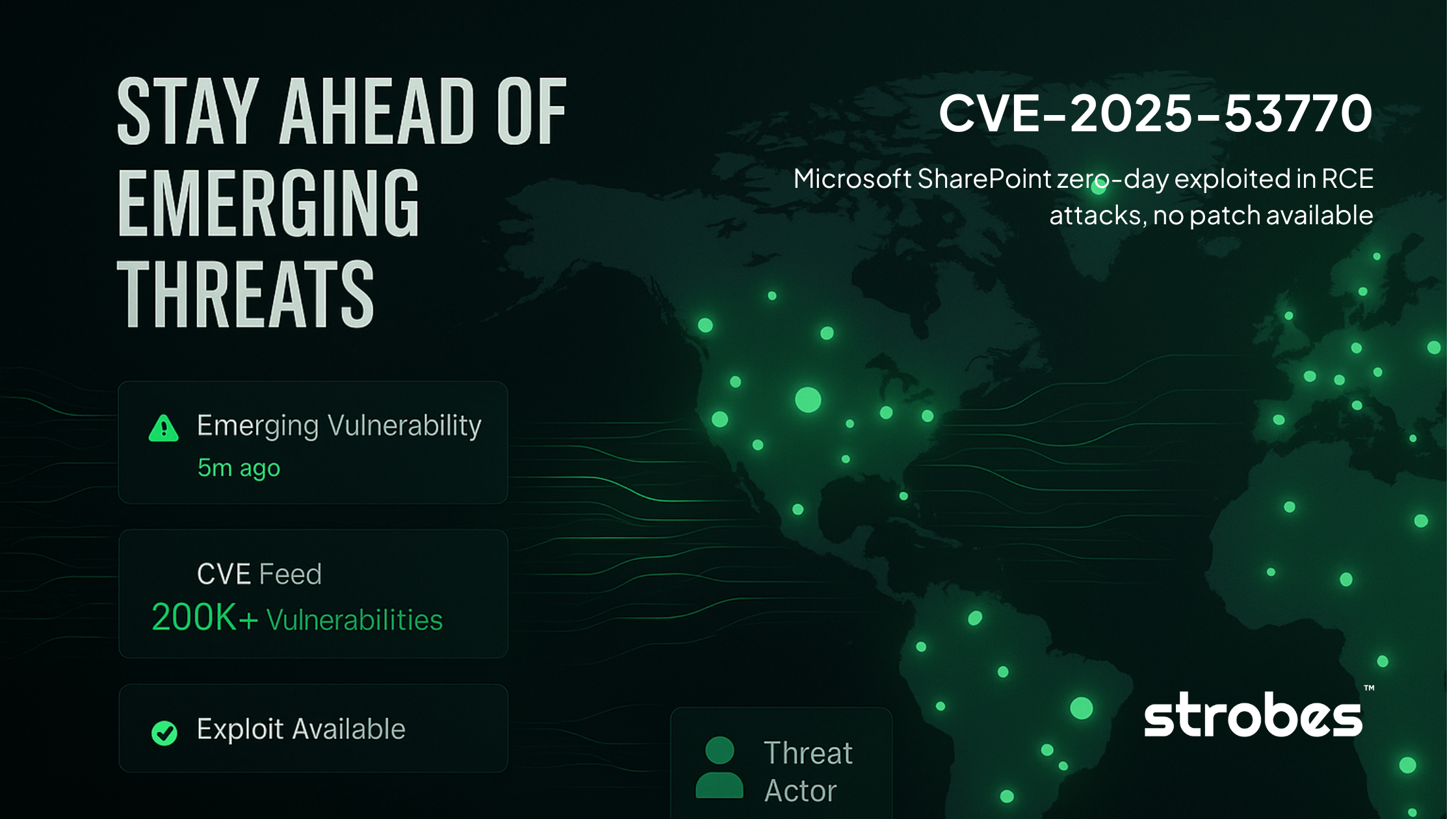
CVE-2025-53770 - Microsoft SharePoint zero-day exploited in RCE attacks
CVE-2025-53770 is a critical remote code execution vulnerability (CVSS 9.8) in on-premises Microsoft SharePoint Server that allows unauthenticated attackers to completely compromise servers through deserialization of untrusted data. The Microsoft SharePoint Zero-Day vulnerability is currently being

Why Attack Surface Analysis Must Be Your #1 Priority in 2025?
Enterprises today operate in environments where their digital footprint grows faster than their ability to secure it. As cloud adoption, API integrations, remote work, and third-party partnerships expand, attack surface analysis is now critical for gaining full visibility, uncovering hidden risks, a

Attack Surface Monitoring - Stop Chasing Alerts, Start Managing Risk
Modern enterprises are facing an unprecedented challenge, attack surfaces are growing faster than they can be secured. Without attack surface monitoring, cloud services, SaaS tools, third-party integrations, and remote work only accelerate this sprawl. A recent report found that 62% of organizations
Exposure Management vs Vulnerability Management - The Truth No One Tells You
Enterprises have poured time and resources into vulnerability management programs. Scanners sweep across networks and clouds, producing endless lists of issues to patch. On paper, this feels like control. In practice, teams are overwhelmed and attackers keep finding ways in. Vulnerability management

What Is Threat Exposure Management? A Guide for Security Leaders
Your organization’s attack surface isn’t what it used to be. Cloud workloads, third-party vendors, and remote employees have expanded it far beyond traditional boundaries. Every day, new risks emerge, some visible and many hidden, making it harder to know where you truly stand. Yet most vulnerabilit
Top 6 Data Breaches in June 2025 That Made Headlines
Data Breaches in June 2025 left behind a string of major incidents that exposed sensitive information and interrupted services across industries. From global airlines to municipal governments and investment platforms, no area was untouched. Hawaiian Airlines faced an internal systems disruption, Zoo
What is Network Penetration Testing?
The firewall was set up. Scanners were running. Everything looked fine. Until a routine network penetration test found an old staging server no one remembered. It was still connected, still exposed, and still using a weak password from two years ago. RDP (Remote Desktop Protocol) was open, and withi

Top 5 High-Risk CVEs of June 2025
Each month brings a flood of vulnerability disclosures. But only a few truly matter. The ones being exploited. The ones buried in critical systems. The ones that could take down your environment. In this post, we’ve pulled together the top CVEs of June 2025 not based on volume, but based on risk. Re
How to Tame Your Multi-Cloud Attack Surface with Pentesting
Let’s face it most organizations aren’t using just one cloud provider anymore. Maybe your dev team loves AWS. Your analytics team prefers GCP. And someone else decided Azure was better for access controls. The result? A multi-cloud setup that’s great for flexibility but a nightmare for security and