
Why Deduplication Is the Most Underrated Security Control
Likhil ChekuriFebruary 3, 202612 min read
TL;DR
Security teams face constant pressure from an overload of alerts and findings. Deduplication as a Control Not a Feature Vulnerability deduplication should be treated as a core control in security frameworks, not an optional add-on in tools.
- More findings do not always mean more risks; they often signal redundancy.
- Teams end up reacting to echoes rather than the root problems.
- This leads to inefficient use of time and resources.
1. What Deduplication Means in Security Operations
In security operations, vulnerability deduplication refers to the process of identifying and consolidating repeated vulnerability reports from various sources. Unlike data storage, where deduplication saves space, here it focuses on cleaning up assessment outputs to avoid redundant work.- It targets reports from scans, tests, and audits.
- The process uses matching logic to link similar entries.
- Outcomes include a streamlined view of threats.
- Multiple scanners might detect the same weakness in an application or system. For example, one tool flags a misconfiguration in a web server, and another does the same during a separate scan, creating two entries for one issue.
- Findings repeat across environments, such as development, staging, and production, where the same code base carries the same flaws.
- Retests after fixes can generate fresh alerts if the underlying problem persists or if tools interpret results differently.
- Rules can include hash comparisons or attribute matching.
- Context retention ensures no information loss.
- Unified views speed up analysis.
Types of Deduplication:
Deduplication is commonly described as a data efficiency technique, but its role in security is often missed. By collapsing repeated data into a single source of truth, deduplication limits unnecessary data spread and brings order to environments overloaded with copies of the same information. To understand why this matters for security outcomes, it helps to break deduplication into its core types.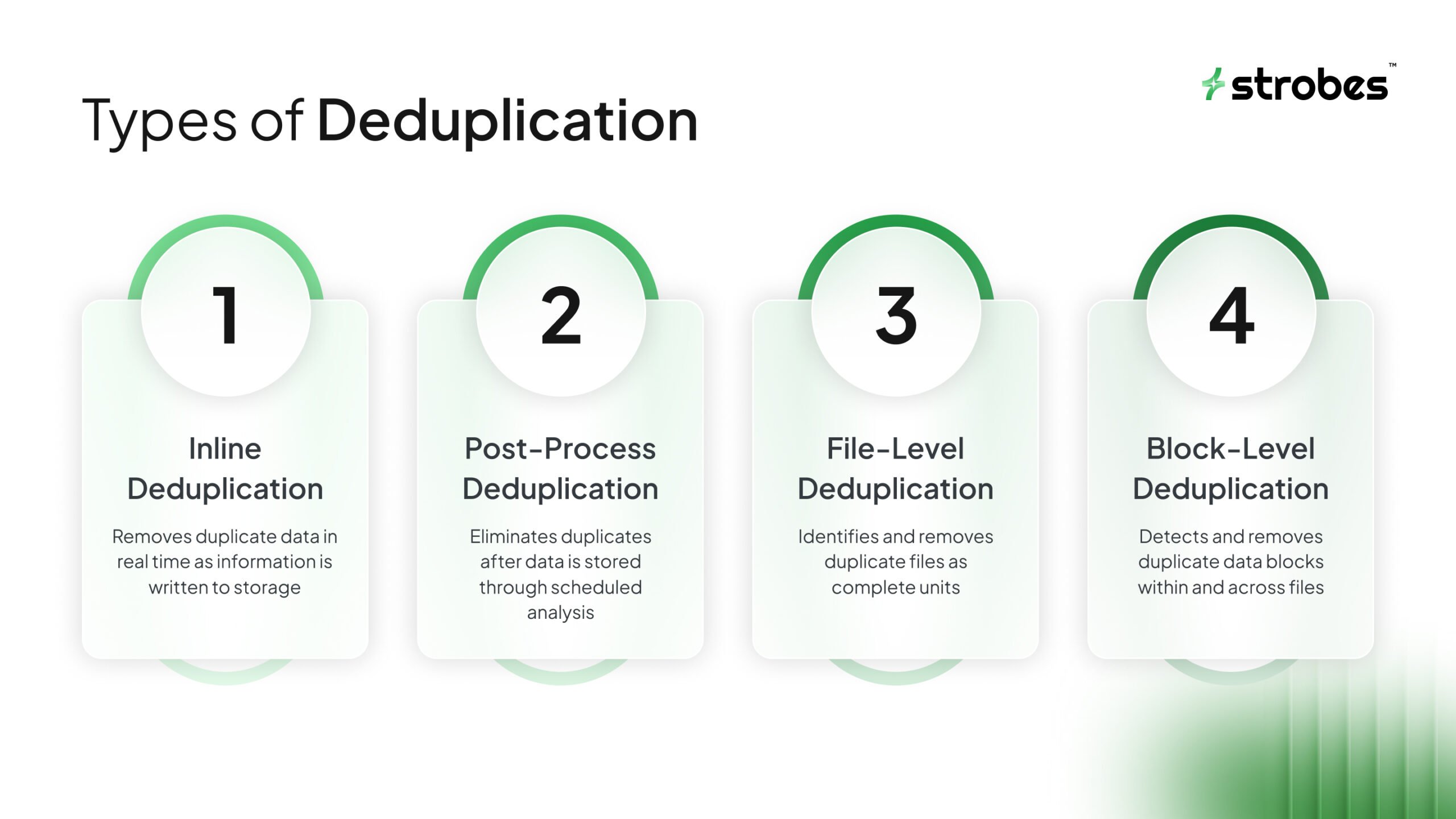
Inline vs Post-Process Deduplication:
The main difference between these approaches is timing. Each affects performance, resource usage, and how quickly risk is reduced.Inline Deduplication:
Inline deduplication works at the point of ingestion. As data enters a system, it is checked against existing data. If a match exists, only a reference is stored. Why teams use it- Prevents duplicate data from being written at all
- Keeps storage growth under control from day one
- Fits continuous data streams such as backups or telemetry
- Requires real-time processing
- Can add overhead if systems are not sized correctly
Post-Process Deduplication:
Post-process deduplication runs after the data is written. Full copies are stored first, then consolidated later through scheduled jobs. Why teams use it- Keeps ingestion fast
- Works well with existing systems and historical data
- Allows resource-heavy processing during low-usage periods
- Duplicate data exists until cleanup completes
- Storage use and exposure remain higher during that window
File-Level vs Block-Level Deduplication:
This distinction focuses on how precisely data is compared.File-Level Deduplication
File-level deduplication treats each file as a single unit. If two files match exactly, one is retained and the rest reference it. Strengths- Simple and fast
- Works well for shared repositories and image libraries
- Misses duplication inside files
- Less effective for large or frequently updated data
Block-Level Deduplication
Block-level deduplication breaks data into smaller segments and compares those segments individually. Strengths- Detects repetition inside files
- Delivers higher consolidation rates
- Scales well for large data volumes
- Higher processing and metadata overhead
- Requires careful integrity management
2. How Duplicate Findings Quietly Break Security Programs
Duplicate findings create hidden chaos in security programs. They inflate the backlog, turning a manageable list of 100 unique issues into 500 entries. Teams then spend hours sorting through repetitions instead of fixing problems, leading to delays in addressing actual risks. This volume misleads teams into thinking high alert counts mean high exposure, when often it is just an echo from overlapping tools. The result? Prioritization suffers because everything looks urgent. Operational impacts are clear: Remediation cycles stretch from days to weeks as engineers chase shadows. AppSec and infrastructure teams experience fatigue from constant false urgency, reducing their effectiveness over time. Worse, duplicates erode trust in tools and reports. When dashboards show inflated numbers, stakeholders question the data's reliability. This disconnects security from business goals, where the focus should be on reducing exposure, not managing noise. In the end, organizations miss opportunities to mitigate real threats because resources get tied up in redundancy.- Trust loss affects tool adoption.
- Business alignment suffers from misreported risks.
- Missed mitigations increase breach potential.
3. Severity Inflation Starts With Duplication
Duplication does not just add volume; it amplifies perceived severity. A single medium-risk vulnerability reported multiple times can appear as a cluster of high-priority items, skewing the overall risk assessment.- Repeated reports create false clusters.
- Medium risks look critical in aggregates.
- Assessments become unreliable.
4. Deduplication as a Control Not a Feature
Vulnerability deduplication should be treated as a core control in security frameworks, not an optional add-on in tools. It directly influences key outcomes like accurate risk posture by providing a clean slate for analysis.- Frameworks benefit from built-in cleanup.
- Outcomes tie to program maturity.
- Clean slates enable better planning.
5. Where Deduplication Fits in the Security Lifecycle
Vulnerability deduplication integrates across the security lifecycle to maintain consistency. It starts before prioritization by cleaning raw data from scans, ensuring only unique findings enter the queue.- Pre-prioritization cleanup sets the stage.
- Unique entries simplify queues.
- Consistency aids all phases.
6. Manual Deduplication Fails at Scale
At small scales, teams might handle duplicates manually through spreadsheets or meetings, but this approach collapses in larger setups. As organizations grow, the volume overwhelms human efforts.- Small scales tolerate manual work.
- Growth exposes limitations.
- Volume leads to breakdowns.
7. What Effective Deduplication Actually Looks Like
Effective vulnerability deduplication goes beyond simple matching. It groups findings by root cause, analyzing underlying factors like shared code vulnerabilities rather than surface-level scanner outputs.- Root cause focus deepens accuracy.
- Analysis goes beyond outputs.
- Grouping reveals patterns.
- Asset links ensure relevance.
- Time factors avoid cycles.
- Histories inform decisions.
8. Deduplication and Risk-Based Workflows
Clean data from vulnerability deduplication enables true risk-based workflows. Teams can rank issues based on business impact, exploit likelihood, and asset value without distortion from duplicates.- Clean data supports ranking.
- Factors include impact and likelihood.
- Distortion-free views guide priorities.
- Fixing the right problems first.
- With fewer entries, remediation capacity stretches further, targeting high-exposure areas effectively.
- Quality focus optimizes efforts.
- Capacity extension boosts coverage.
- Patterns inform strategies.
9. Why Deduplication Is Ignored in Most Tool Decisions
Tool selections often prioritize detection capabilities over operational efficiency, leaving vulnerability deduplication overlooked. Buyers chase advanced scanning features, assuming actionability comes later.- Detection trumps efficiency in choices.
- Assumptions lead to gaps.
- Overlooks create imbalances.
- Debt accumulates over time.
- Vendor emphasis misleads.
- Native support sustains programs.
10. Measuring the Impact of Deduplication
To prove value, track specific metrics post-implementation.- Start with a reduction in open findings: a 30-50% drop is common as duplicates consolidate.
- Mean time to remediate improves, often halving as teams handle unique issues faster.
- Fewer reassigned tickets indicate better ownership clarity.
- Finding reductions quantify savings.
- Remediation times measure speed.
- Metrics showcase efficiencies.